Lets straight to the point, I’ll break down this article into 4 sub-chapter:
- The Theory
- The Attack and The Outcome
- The Mitigation
Security Experts says: “Security is as good as layer belows” or “Security is as strong as weakest link”
Dalam 7 OSI Layer…klo dari bawahnya aja udah kena (physical and data link)…keatas2nya juga akan kena (domino effect)
Wokeh, lets prepare the ingredients:
- Manageable Switch (klo pake switch biasa ga keliatan apa yang mau dipraktekin)
- Kali Linux (for me its 2016 version)
- Another PC (I use Kali and Windows in same host a.k.a Virtual Machine)
—————————————-
The Theory
Setiap switch pasti punya yang namanya CAM Table
For you who doesn’t know what CAM table mean, take a look at this pic below

Yup…mac address table
CAM table ini berguna bagi switch untuk switching traffic *yea right man -_-; …
Lah, bener kan…switch itu bahasa indonesianya apa? pengalihan/menukar (if you recall how switch works then you’ll understand that switch is replacing mac-address for each hop both source and destination address)
MASALAHNYAAA…THE PROBLEM IS…. المشكلة
هي… 문제는 (wkwkwk…all same meaning: the problem is)
Setiap switch naro CAM table ini di ASIC chip

And…because of hardware characteristics…there is….a limitation
HOW MUCH MAC ADDRESS CAN BE STORED IN THIS (or THOSE) CHIP(S)?
The answer may vary, switch cisco cat6800 can store 128k mac addresses while cat 2960 only hold maybe 8000 mac addresses
So, what happens when the table goes full? OVERFLOW OF BROADCAST…switch revert to hub (being able to broadcast traffic only), this is the fallback mechanism of switch if its table is full
Anddd that is the goals…broadcast the traffic so we can see what being send and receive, or even worse…bring down the network
———————————–
Attack and Outcome
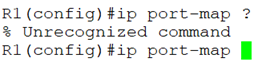
Gw pake cisco cat3750…show mac address-table count menunjukkan bahwa ini switch sanggup nampung sekitar 6000an mac addresses

And start that kali linux…open terminal, just type macof (mac address overflow)

Anddd….now this kali linux will flood the switch with a ton of bogus mac addresses

In a matter of second (ga sampe 5 detik malah), lets see the CAM table again

From the previous 6003 down to 40…that how you bring down the network…
Makanya gw bilang jgn pake switch biasa, ga ketauan mac address table nya abis apa engga/diserang apa kaga nya
Impactnya…?? Ga usa jauh2 untuk bring down network, lets bring another brother of kali, the red hat

Gw pake RHEL 7, ip-nya 10.2.23.23

Trus gw ping ke 10.2.23.1 (gateway)…dan di kali linux gw jalanin wireshark…apply filter ip.addr == 10.2.23.0/24

Now we see the traffic come back and forth…ini baru ping, bagaimana klo dia ngirim sensitive data? Dengan adanya broadcast…attacker can sniff through wireshark
———————————-
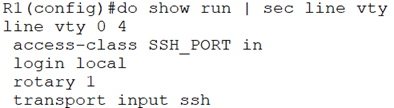
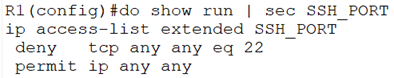
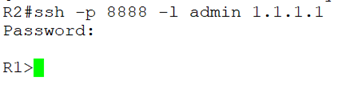
The Mitigation
- Port Security (link)
- An even better solution: shutdown all unused port
That’s it guys…next lets try another network-offensive security attack (if I have time to do that 😉 )
This is going to be my next writing article…network security attack…(N.O.S), do you like it? Leave a comment…