See here (see chapter “Authentication”) if you don’t know about Digital Certificate (a.k.a PKI a.k.a public key infrastructure a.k.a CA a.k.a Certificate Authority)
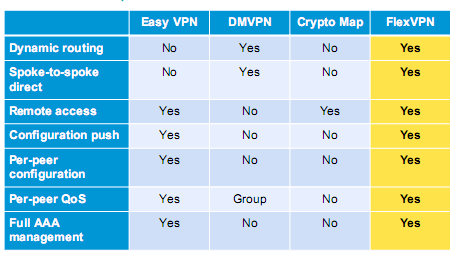
Now the question is…what is FlexVPN?
FlexVPN is Cisco terminology of VPN that can be connected and authenticate via multiple terms (in this case I’ll show you the Digital Certificate ways, VPN biasa juga bisa sih)
FlexVPN Benefits:
- Bisa di deploy di MPLS Network (private or public)
- Can accept both site-to-site and remote VPN at the same time
- Failover Redudancy (can be done via dynamic routing over FlexVPN interface tunnel)
- 3rd party compatibility…this is it…ga harus VPN ama cisco devices juga hahaha
- Multicast support
- Advanced QoS (bisa ditaro langsung pas traffic mau jalan atau di hub router-nya aja)
- VRF awareness, cocok buat ISP
Mudah2an klo sempet kita oprek satu2 ini benefit2nya…bener kaga yang Cisco bilang…
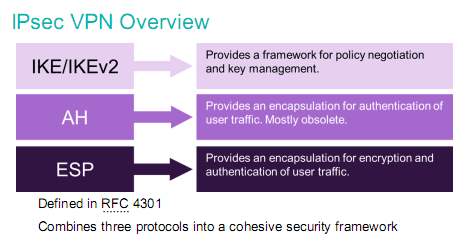
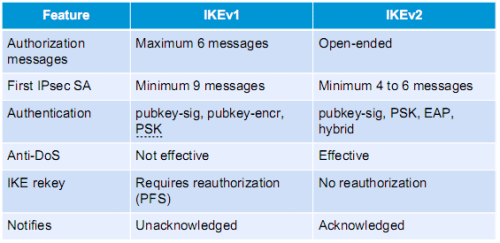
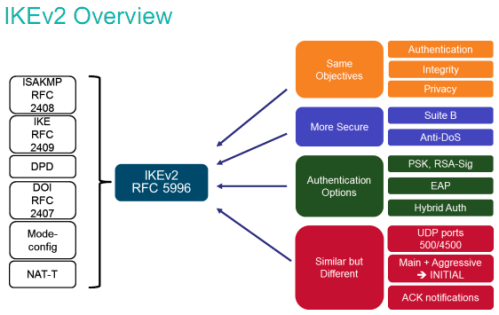
Warning: FlexVPN relies heavily on the powerful IKEv2 (see here) to get it working, that why this VPN is so “flexible”…so, get you’re a** down to the new successor of ISAKMP and IKEv1…
Note: IOS 7200 15.4 ga lengkap config PKI server-nya, gw pake 3640 yang lama (surprisingly complete configuration about PKI server…)
DAN GUA BARU TAU TERNYATA ROUTER CISCO BISA JADI PKI SERVER!!! Gua kira harus pake VMware isi Windows Server….
——————————————–
The Idea and Network Design
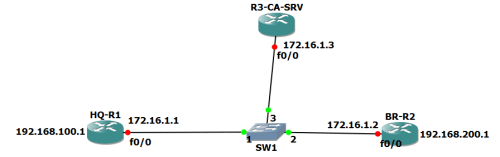
Jadi HQ-R1 akan konek dengan BR-R2 via VPN…awalnya pake pre-shared-key (PSK), nanti kita ganti pake digital certificate (minta dari R3)
————————————————-
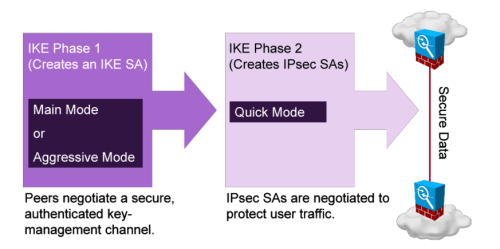
Configure IKEv2 first on both Routers
On HQ-R1 (and BR-R2 with necessary changes)
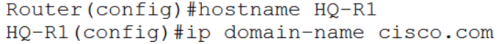
First…the hostname and domain (kepake nanti buat Digital Certificate, wajib ada hostname sama domain soalnya)
Second…Configure IKEv2 Keyring
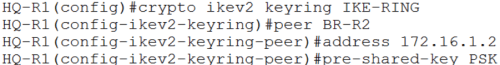
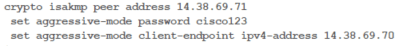
Awalnya kita pake pre-shared-key untuk konek vpn (passwordnya “PSK”)
Third…Configure IKEv2 Profile
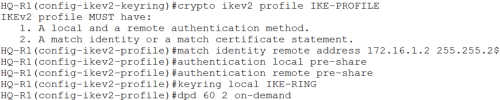
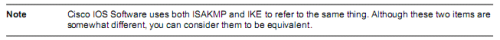
IKEv2 bisa asymmetric authentication (dia/local pake PSK, klo remote pake yang lain…kasus diatas sama2 pake PSK)
DPD (dead peer detection)…fitur yang include secara default di IKEv2 framework untuk ngedeteksi peer/ujung yang satu VPN-nya mati, 60..intervalnya, 2…nyoba 2x, on-demand…ya klo lagi butuh (ada settingan periodic kok)
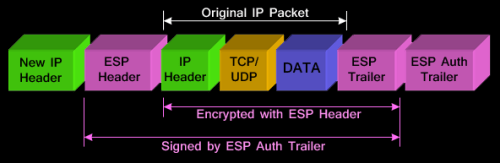
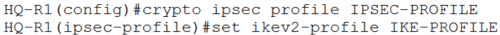
Fourth…Configure IPsec profile with IKEv2 profile we created before
Fifth…Configure interface tunnel for private traffic and attach that ipsec profile in, don’t forget that ip route too
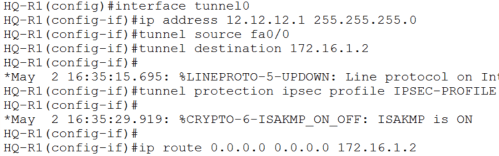
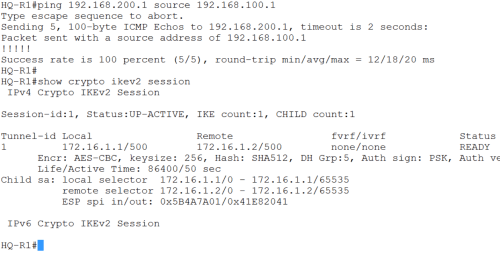
Verification…ping from loopback R1 (100.1) to R2 loopback (200.1) and type “show crypto ikev2 session” untuk liat ada IKEv2 proses ga pas lagi ping-pingan
——————-
Configure certificate on R3-CA-SRV
Now….im actually amazed by Cisco Router to act like CA Server…lets see the configuration
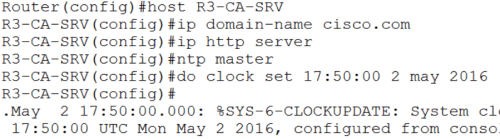
Untuk jadi CA ada beberapa hal yang harus diperhatikan
- Ganti hostname
- Harus ada domain-name
- Harus di set NTP (atau minimal clock-nya dibenerin)
- Enable http…soalnya request certificate-nya dari port 80 (klo lo pernah setting2 PKI/CA di windows…pasti lu ngerti)
- Settingan CA-nya…with crypto pki server [nama SERVER] seperti dibawah ini:
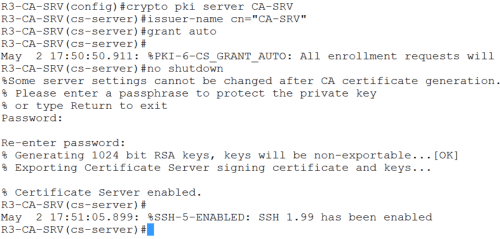
Kasi password (contoh: cisco123), jadi klo ada yang mau minta request dibikin sertifikat (kek kita minta KTP ke kelurahan, istilahnya: ENROLL) harus tau password-nya
Jangan lupa di “no shutdown” untuk aktifin CA-nya
————————————————————————–
HQ-R1 enrollment to CA-SRV and change the authentication method from PSK to Digital Certificate
Ceritanya HQ-R1 minta dibikinin sertifikat ama R3-CA-SRV, soalnya dia mau konek VPN-an ama BR-R2, biar ga pake PSK (jablay?!?) lagi…
Klo pake PSK kan masalahnya pasti itu2 aja…kebanyakan PSK…kena raja singa…
Maksudnya…klo mau ke R2 pake kunci A, klo mau ke R3 pake kunci B, klo mau ke R4,R5,R6,R7..dll??…gantungan kunci kita bawa (not preferable with Company with many branch)
First…bikin dulu path ke R3-CA-SRV buat request certificate
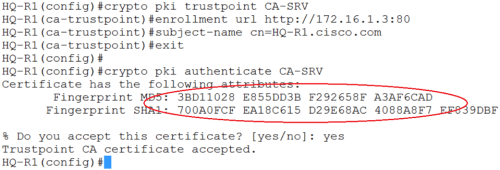
Look at keyword enrollment…pake URL ke port 80 (that’s what I mean enable http in R3-CA-SRV)
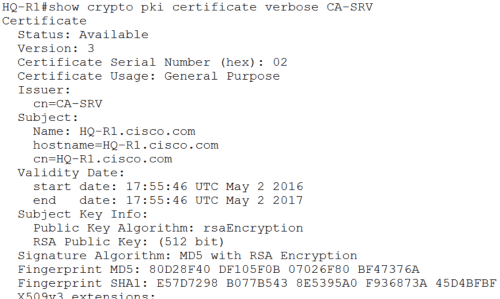
Trus ketik “crypto pki authenticate [nama CA]“…klo berhasil nanti R3 akan ngasi certificate dengan fingerprint unique punya dia
perhatiin Fingerprintnya…sama ga (nanti pas di BR-R2 kita bandingin)
Second, enroll…minta bikinin sertifikat dongss pake “crypto pki enroll [nama CA]”
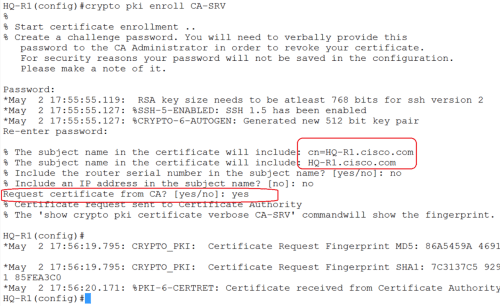
Nanti ada beberapa pertanyaan…intinya pas “request certificate from CA“…ketik “yes”
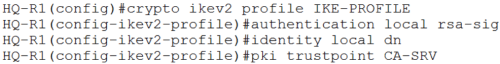
Now…lets change HQ-R1 authentication method to RSA-SIG (digital certificate) from trustpoint CA kita and with identity pake dn (distinguished name…itu tu…HQ-R1.cisco.com)
And then…Verification
——————————————————————————-
Change authentication behavior BR-R2 using Certificate if HQ-R1 wants to connect
Pretty much the same…tentuin CA path-nya
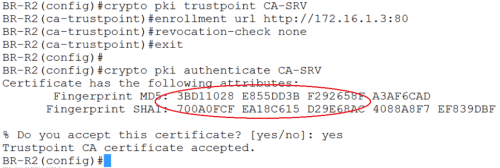
See…FINGERPRINT-nya sama kan kek HQ-R1…(check sendiri konfigurasi R1 diatas)
Trus…bikin certificate map…biar klo ada mau konek ke BR-R2, pake metode yang ada certificate map itu…trus masukin deh itu map ke IKEv2 profile-nya
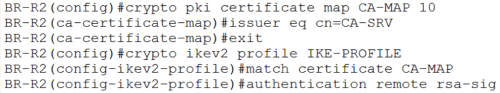
kita bisa liat diatas…klo ada yg mau konek ke BR-R2, tolong tunjukin certificate-nya, dan dia hanya percaya sama certificate yang dari CA-SRV yang kita tunjuk tadi
————————————-
Verification
Shut and then no shut int tunnel-nya, biar refresh ulang IKEv2 negosiasinya
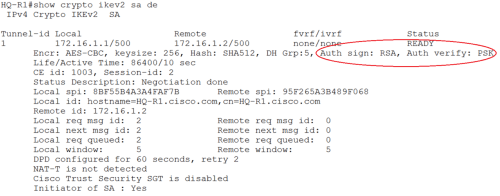
Di HQ-R1…dia mau VPN ke BR-R2 pake RSA…
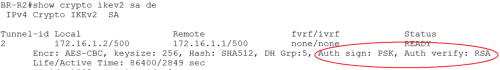
Dan di BR_R2 (gambar dibawah)…klo ada yang mau konek pake verifikasi RSA…
And…im done
———————–
References:
http://www.cisco.com/c/en/us/support/docs/security/flexvpn/115782-flexvpn-site-to-site-00.html