What we are going to learn
- The theory of IKEv2
- How to configure IKEv2 site-to-site VPN with Cisco Router (IOS v15 mandatory)
- How to configure IKEv2 site-to-site VPN with Cisco ASAv
- Hopefully, how to develop it using Juniper Junos and with vSRX (part 2, coming soon)
Requirement:
- GNS3
- IOS 15 (search: C7200-ADVIPSERVICESK9-M Version 15.2(4), google it yourself)
- ASAv .vmdk (same, look it up yourself)
- WinXP VM .vmdk (same, but you can use your loopback interface if you wish)
Prerequisite for learning:
- VPN knowledge
- ASA basic configuration
———————
The Idea
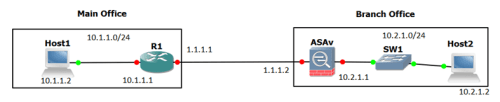
Design
—————————
What is IKEv2? Even more…what is IKE itself??
Ada baiknya baca kriptografi fundamental dulu…but if you want to skip, I’ll explain it to you briefly
Before IKE, there was ISAKMP (Internet Security Association and Key Management Protocol)…sebuah protocol yang berisi framework bagaimana cara mengatur SA (security Association) dan metode2 kriptografi di jaringan
Apa itu SA? Parameter2 seperti hashing, enkripsi, authentikasi, dsb yang harus dipenuhi dan disepakati oleh kedua belah pihak (peer) untuk bikin VPN
Nah, protocol ISAKMP itu hanya untuk securing “channel”nya (jaringannya saja, phase 1), dengan IKE kita bisa securing traffic-nya juga (with IPsec, phase 2)
So, ISAKMP is a part of IKE, and IKEv2 add more robustness to Key Exchange mechanism…one of them is by supporting EAP (Extensible Authentication Protocol) by default, itu loh yang digunain ama 802.1x alias EAP over LAN alias EAPOL, yang pake AAA Server itu
Sebenernya banyak lagi keunggulan IKEv2, hanya saja gw sendiri ga terlalu dig deeper, perbedaan lebih banyak bisa dilihat disini
And last…IKEv1 dan IKEv2 not compatible with each other…
Eh…IKEv1 config-nya yang kek mana? Ya itu…yang site-to-site VPN biasa…itu IKEv1 (yang securing DMVPN gw waktu itu pun termasuk IKEv1)
——————————-
The Configuration
IKEv2 ada beberapa step…
- Bikin domain sama rubah default hostname
- Bikin ACL, bikin list IP-IP mana aja yang bisa VPN (important note ada dibawah)
- Bikin Proposal, ini kek ISAKMP-nya IKEv2
- Bikin Policy, kita bikin policy yang dimana policy itu ada proposal-nya
- Bikin Keyring (gantungan kunci?!?)
- Bikin Transform-set, settingan IPsec-nya
- Bikin Mapping, join all pieces above together
- Mapping itu IKEv2 ke interface, ke outside/peer tentunya
On Cisco Router (mau bikin site2site VPN antar router juga bisa pake contoh ini)
Pertama2, ganti hostname dan domain dulu…
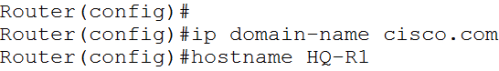
The truth is, gw juga ga tau apa hubungannya domain & hostname dengan IKEv2 (di GNS3 dengan IOS yang gw punya…entah kenapa klo ga pake 2 command ini, ga jalan IKEv2-nya)
Next, the Access-list
Important: jangan bikin “permit ip ANY ANY“…kadang suka ga jalan (I learned it the hard way *Sad*), biasain spesifik bikinnya
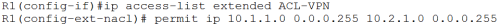
The Third one is, The Proposal
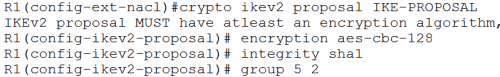
Biasa…nego2 dulu sama peer sebelah…gw maunya pake enkripsi ini, pake hashing anu…harus sama satu sama lain
encryption: bikin data ga bisa dibaca
integrity: bikin data ga bisa dirubah
group:…ini diffie-hellman algorithm…untuk secure key exchange, angka 5 dan 2 itu tingkat kesulitan algorithmanya (dont ask me the detail, i dont know either lol)
The Fourth One is, Policy

Ibarat kata, klo mau pake IKEv2…harus ada policy (dimana policy-nya pake proposal yang kita buat tadi)
And the Fifth one is, define Keyring
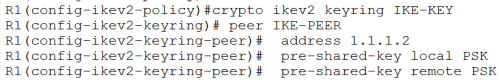
Konsepnya memang gantungan kunci…kunci A buat pintu A, kunci B buat pintu B, dimana Peer = Kunci (Peer Branch = Kunci ke Branch), semuanya dikumpulkan di…gantungan kunci wkwkwk
And the Sixth one is, Transform-set
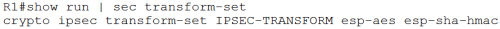
Transform ini untuk IPsec yang mau kita gunakan apakah mau pake encapsulating security payload (esp) yang mana…disini gw pake aes untuk authentikasi dan pake sha512-hmac buat hashing key-nya
Next, the Seventh one, Profile
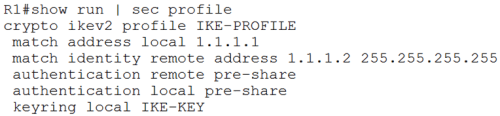
Kita bikin profile, klo mau ke peer pake authentikasi model apa (match address local sama identity remote address), disini gw pake pre-shared-key
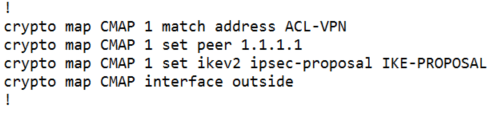
And the eighth one, joining all pieces together…Mapping
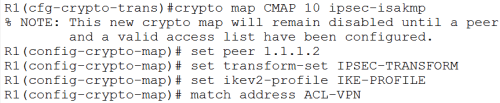
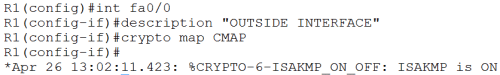
And last, taro itu crypto map di interface OUTSIDE alias yang ke WAN alias yang kearah Peer VPN kita
On ASA
Untuk ASA sebenernya ada Site-to-Site VPN Wizards-nya, but im not gonna do that way (menyusahkan diri sendiri sih)…in case of some troubleshooting…
(Disclaimer: entah kenapa kadang IKEv2 nya ga jalan…gw konfig IKEv1 dulu trus bikin IKEv2 baru tuh traffic jalan, termasuk di Router-nya juga, kek ga mau “ngangkat” gitu VPN-nya…pas IKEv2 udah jalan, gw apus yg IKEv1 masih normal2 aja, let me know why that happen)
Step2-nya adalah
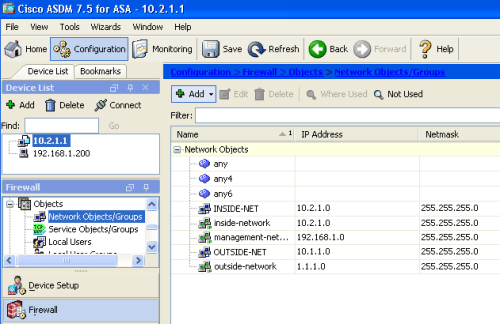
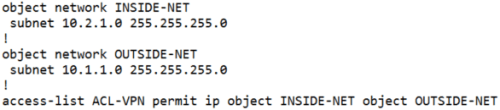
- Bikin Object group dulu (contoh: INSIDE-NET Object buat network 10.2.1.0-nya kita)
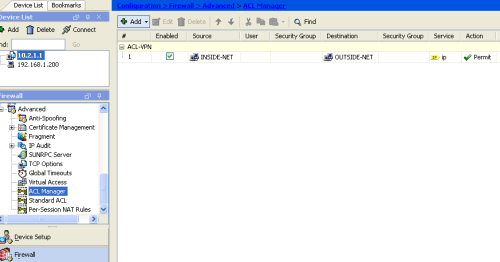
- Bikin ACL, biar INSIDE object (yg isinya network 10.2.1.0) bisa ke OUTSIDE (bikin juga object ini, ke 10.1.1.0)
- Routing nya jgn lupa (biar bisa ping lah -_- )
- Bikin IKEv2 Policy dan Proposal
- Pastikan koneksi IKEv2 dari luar di enable
- Bikin group policy sama tunnel group
- Dan bikin crypto-map nya
On Firewall Menu Configuration (Object network & access-list)
On Configuration (next to Home icon) > Firewall > Objects > Network Objects/Groups > add
Trus ke Firewall > Advanced > ACL Manager > add
Versi CLI-nya (I know some of you are “CLI-freak” hahaha)
trus ke Device Setup menu untuk setting Routing-nya
masuk ke Device Setup > Routing > Static Routes > add
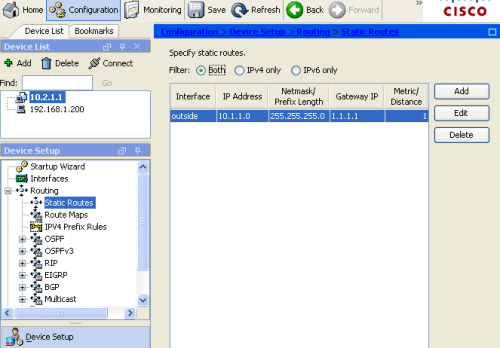
Versi CLI-nya:”route outside 10.1.1.0 255.255.255.0 1.1.1.1” (pendek ya, daripada klak klik ga jelas, that’s why I know some people prefer the “old fashioned way”)
Trus bikin Policies-nya di Site-to-Site VPN menu
Site-to-Site VPN > Advanced > IKE Policies > add (IKEv2 policies)
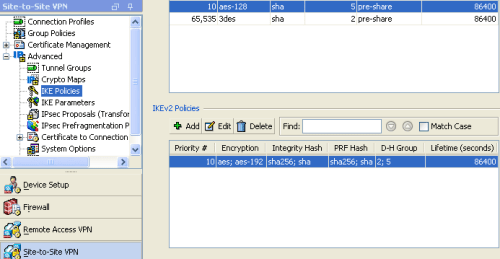
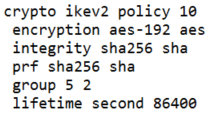
Versi CLI:
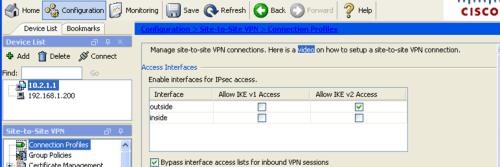
Jgn lupa di centang “Allow IKEv2 Access” (klo pake cli:”crypto ikev2 enable outside“, gambar dibawah ini)
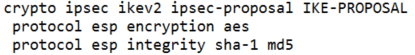
Next, the proposal…Site-to-Site VPN > Advanced > IPsec Proposals > add (IKE v2 IPsec Proposals)
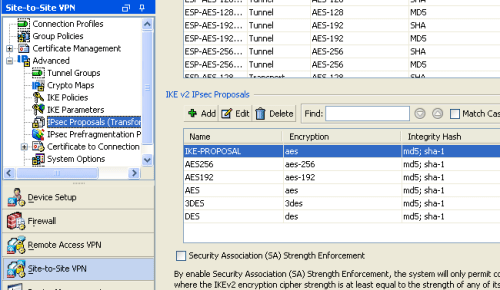
Versi CLI:
Trus configure group policy-nya…klo mau konek ke peer 1.1.1.1 pake tunnel apa (ikev1/ikev2)
Site-to-Site VPN > Group Policies > add
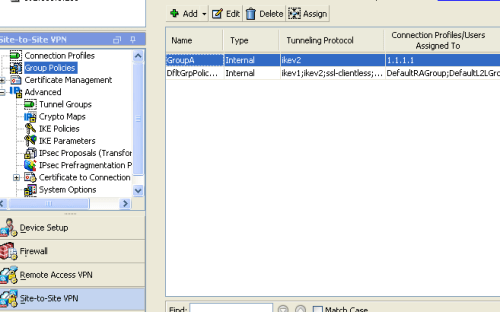
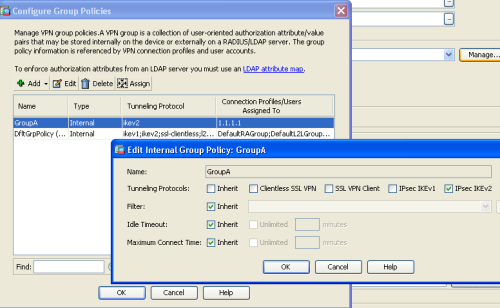
The CLI way:
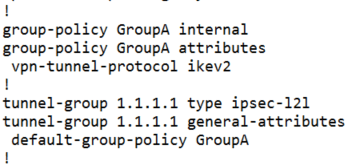
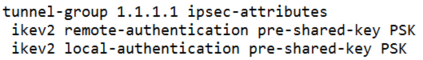
Trus configure tunnel-group-nya on Site-to-Site VPN > Advanced > Tunnel Groups > add
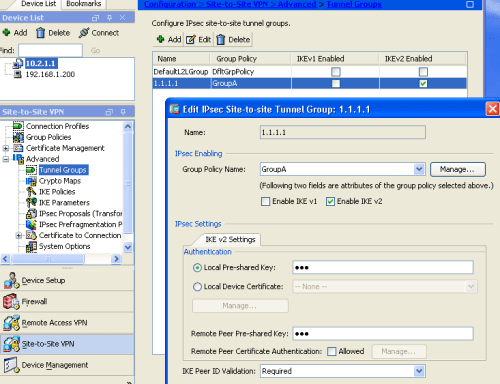
The CLI way:
Last, define crypto map, Site-to-Site VPN > Advanced > Crypto Maps > add
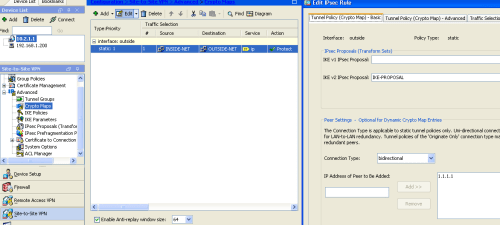
The CLI way:
————————————————————————–
Verification
On Router, we can type “show crypto session”
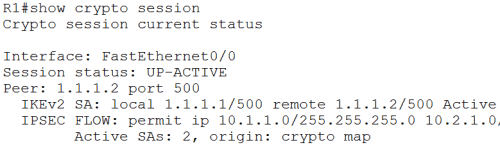
Alrite, IKEv2 is UP and ACTIVE
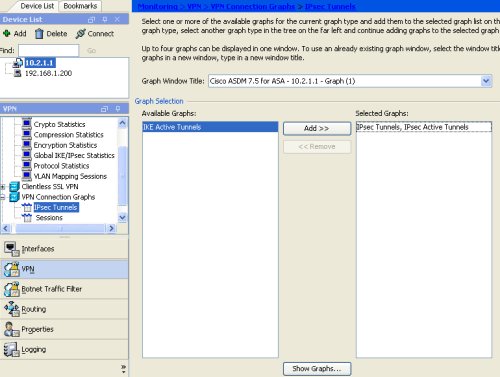
On ASA…masuk ke Monitoring > VPN > VPN Connection Graphs > IPsec Tunnels (atau sessions juga bisa)
screenshot pingnya lupa gw pasang, nanti klo ada waktu gw tambahin
——————————————-
References:
https://www.fir3net.com/Firewalls/Cisco/cisco-how-to-configure-an-ikev2-site-to-site-vpn.html
http://rockhoppervpn.sourceforge.net/techdoc_ikev1vsikev2.html
Keith Barker SIMOS cbtnuggets video


Leave a comment