Well, another one of my note that left behind, I’ll make sure this one goes to my blog as well…
Gua buat catetan ini karena banyak konfigurasi yang ga ngerti pas lagi buat VPN…
“ini command buat apaaa…kenapa harus adaaa…dsb dsb…”
Make sure you read my basic VPN article first
———————————————————-
VPN Networking Protocol, the basic
There are 4 main protocols:
- PPTP (Point-to-Point Tunnel Protocol), metode agar gimana caranya client/workstation bisa konek ke VPN (kek remote VPN gitu)
- L2TP (Layer 2 Tunnel Protocol), metode agar gimana caranya Main Office Network bisa konek ke Branch Office network via ISP tapi dengan skema IP yang sama/network yang sama (contoh: main network pake IP 10.1.1.0~10.1.1.200, nah branch network tinggal make ip sisanya sampe 10.1.1.254…seakan2 nge-LAN gituh…walaupun beda wilayah)
- IPsec (IP Security)…metode enkripsi untuk layer 3 (IP – internet Protocol)
- SSL (Secure Socket Layer)…metode enkripsi untuk layer 4 keatas
Like I said…VPN networking protocol (Layer 3 in OSI Layer)…
The difference? I’ll explain it to you simply in one line: PPTP < L2TP < SSL < IPsec
Yang gunain PPTP rata2 adalah Microsoft Client (using Microsoft Windows Platform) and this protocol is a weak one (but easier to use and configure), link
Yang gunain L2TP rata2 adalah ISP…kelemahannya adalah Layer 3 ga dienkripsi (untuk itu biasanya digabung sama IPsec)
Yang gunain SSL adalah remote user untuk Remove VPN, user2 hanya perlu komputer yang support “HTTPS” (clientless, ga perlu install macem2, cukup browser aja)
Yang terakhir yang paling bagus adalah IPsec (RFC 4301)…jeleknya adalah settingannya aga banyak, plus harus disetting on both side of network, that’s why SSL more preferable in common user
——————————————————————
So…IPsec huh?
IPsec is quite complex (that’s why it secure…), why?
- Because there must be some policy how to exchange and manage the key
- Because there must be some protocol that can authenticate traffic
- Or, there must be a protocol that CAN both encrypt and authenticate the traffic
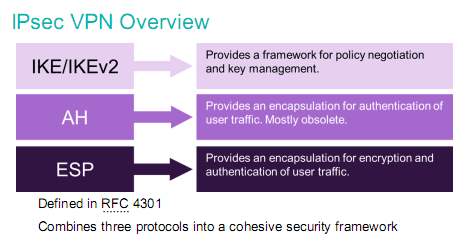
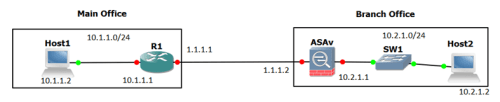
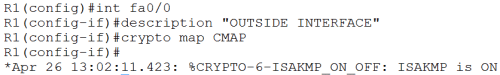
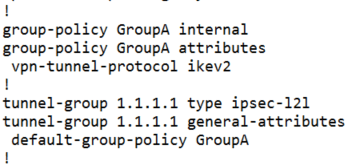
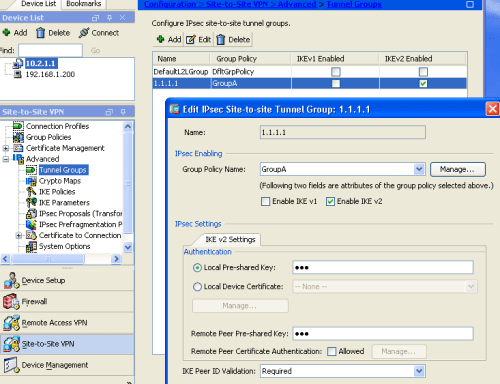
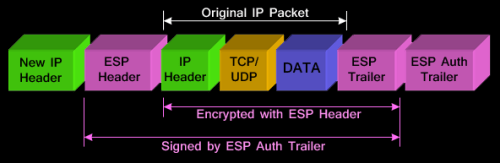
From seeing above image, you’ll understand what I mean…
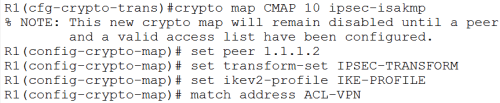
So, dalam membangun VPN terutama site2site…settingan IPsec pasti ada…
This guy itself support 2 encryption modes:
- Transport mode: encrypt only payload (data), header ga diutak atik
- Tunnel mode: default, more secure, header packet (inget…yg CCNA, PDU layer internet apa pada TCP/IP protocol?!?) juga di enkripsi
——————————————————–
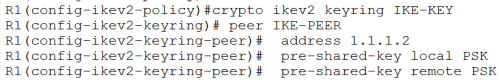
Key Management, Policy, and Negotiation
Yup…we’re talking about IKE* (Internet Key Exchange)
Yang namanya VPN pasti ada tuker2an kunci (traffic VPN kan di enkripsi…cara buka-nya gimana…validasi peering VPN-nya juga gimana)
Nah, kita membahas how IKE works…
This protocol consist of 2 phase
-
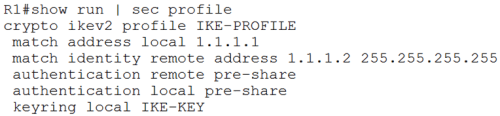
Phase 1 (ISAKMP* Phase):
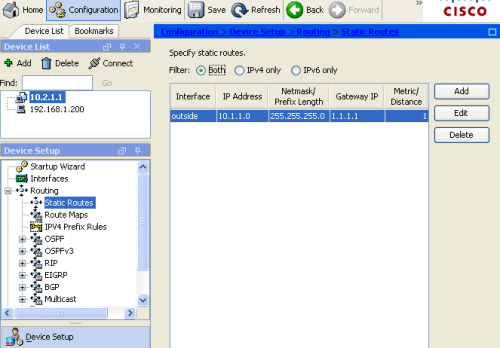
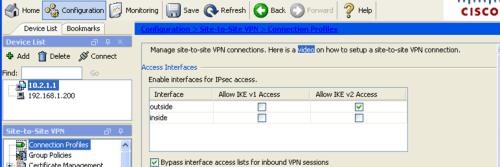
- Specify gateway addresses (local ip buat VPN gateway traffic inbound dan remote ip VPN gateway traffic outbound)
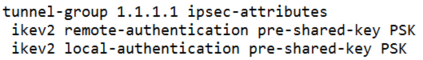
- Specify authentication…mau pake PSK* (pre-shared-key) atau mau pake Digital Certificate* (via CA*/PKI*)
- Specify NAT-T* (NAT Traversal)
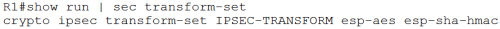
- Specify Transform-set*
-
Phase 1 ada 2 mode:
- Main Mode: more secure but slower…commonly used
-
Aggressive Mode: fast without encryption…biasanya klo salah satu IP Gateway ada yang dinamis, contoh:
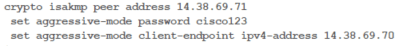
- All of those parameter above is called SA*
Don’t worry…I’ll explain those Terminology used in this article on the bottom chapter
-
Phase 2 (IPsec Phase):
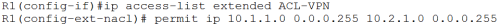
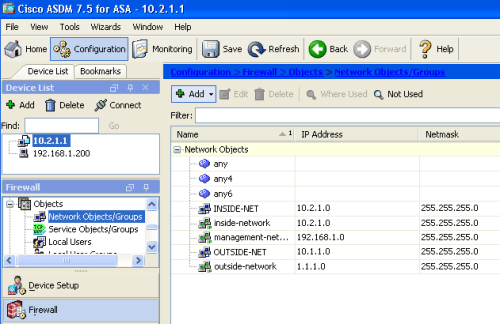
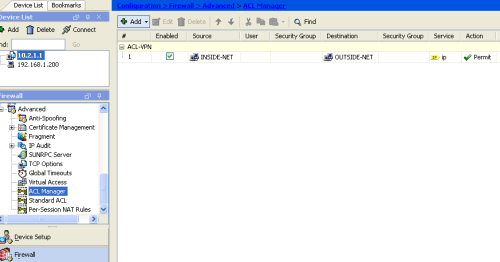
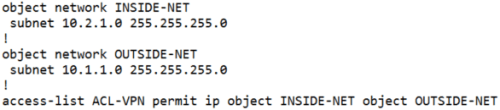
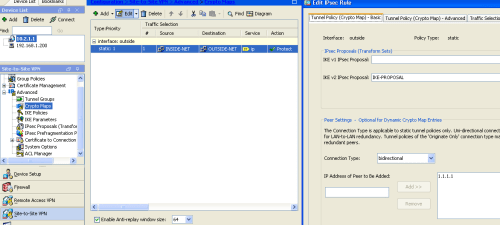
- Specify what traffic/network go through VPN (Access-list anyone?!?)
- Specify the use of PFS*
-
Specify the proposal
- authenticate and encrypt the traffic (ESP* – Encapsulating Security Payload)
- or authenticate only (AH – Authentication Header), better performance-less secure
- or both of them…AH and ESP (not common anymore, everyone prefers ESP now)
- Specify Expiry Date…for Key and Session
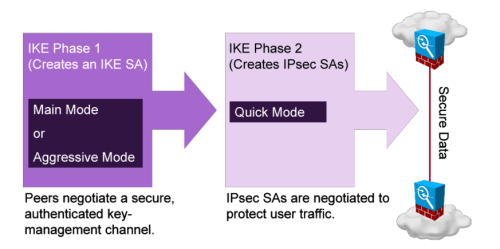
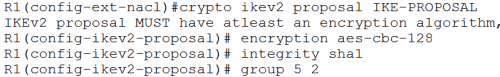
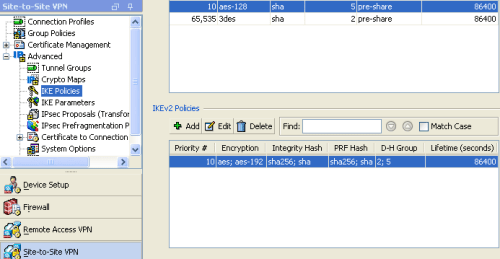
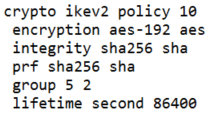
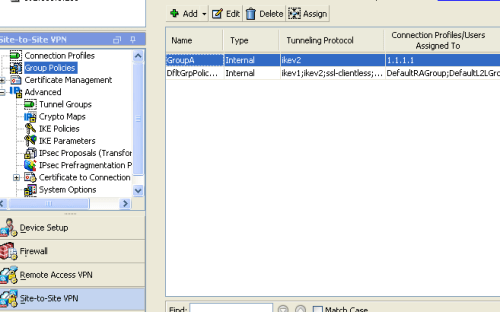
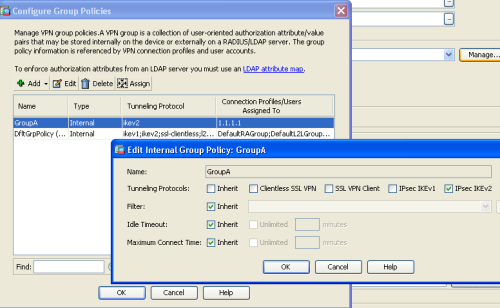
Nah, IKE itu ada 2 versi…versi jadul yaitu IKEv1 dan versi robust and flexible one which called IKEv2
—————————————————————
IKEv1 and v2
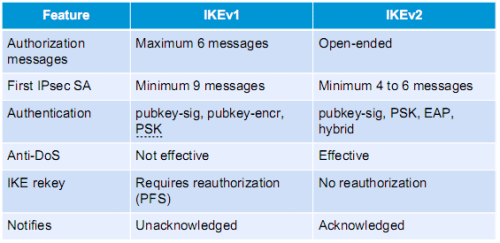
IKEv1
- Defined in RFC 2409
- Use UDP port 500
- Using “Phased” approach (ISAKMP – RFC 2408 on phase 1)
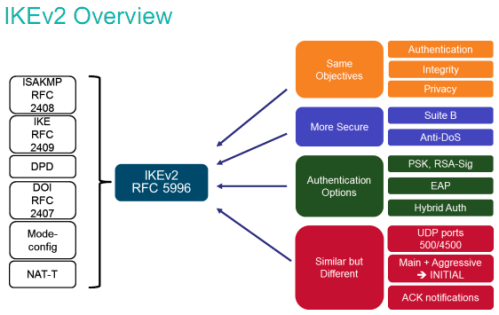
IKEv2
- One of the document is RFC 4306 and RFC 5996
- Same…use UDP port 500, and port 4500
- Not backward compatible to IKEv1
- Using Child SA instead of phase
- Fewer exchanges data to form than IKEv1
- Has built-in DPD*
- Resistant to DoS attack because of cookie mechanism
- Has built-in NAT-T
- Can be used with EAP*
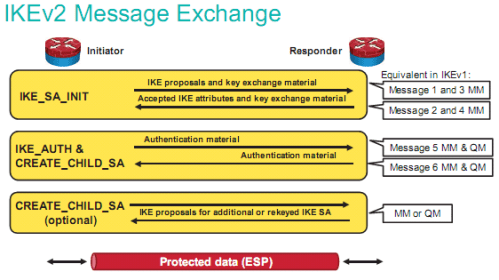
3 steps in IKEv2 exchange messages:
- IKE_SA_INIT: tuker2 proposal SA sama peer, klo match…ke step selanjutnya (klo di IKEv1, mm-main mode alias phase 1-nya udah 4x bolak balik transaksi peering VPN)
-
IKE_AUTH & CREATE_CHILD_SA: authentikasi peers dan bikin child SA (ini kek Phase 2 di IKEv2, qm-quick mode)
- CHILD_SA ini berguna untuk notifikasi peer mati, keepalive, authentication message, bikin key baru/rekeying dll
- Klo ga ada child_sa, berarti balik lagi ke phase 1…repot
- Ini artinya lebih cepet connect/reconnect-nya
IKEv2 provide better DoS prevention
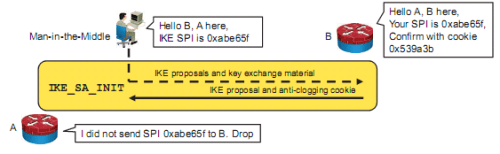
Di IKE…hacker bisa ngirim SPI* (lets say peer initiation) to victim router with many spoofed IP address, hasilnya…consume CPU resources karena banyak “half open” initiation yang masuk, klo ga ada mekanisme prevention DoS…maka ketika victim router establish connection ke router peer DENGAN SPI/KEY YANG DIKASI HACKER…wassalam, ketauan semua isinya, soalnya hacker bisa generate sendiri key-nya (orang dia yang bikin) plus bisa decrypt traffic pake kunci itu
Di IKEv2, mereka pake cookies pas pertama kali peering VPN (ada semacam fingerprint lah)…jadi klo hacker ngirim SPI intended for man-in-the-middle attack…si victim router tinggal ngomong…”bener ga lu ngirim ginian?“
Ke router asli-nya….karena router asli-nya punya cookie pas pertama kali peering…tinggal di cek…klo salah, di drop
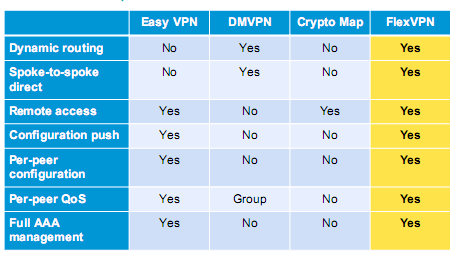
Nah, di Cisco…mereka punya teknologi yang bernama FlexVPN* that relies heavily on IKEv2…
—————————————————————
Terminology
ISAKMP (Internet Security Association and Key Management Protocol): this is a framework…of protocol, kek lu mau masuk ke istana Negara…pasti ada protocol yang harus dipenuhi sebelum lu bisa masuk, nah protocol2 itu kan ga Cuma 1…pasti ada parameter2 lain yang harus dipenuhi. Kumpulan protocol2 ini di VPN dinamakan SA (security association)
Framework: i might have to explain this because I’ve used this words many times…klo protocol itu aturan, nah framework itu adalah kumpulan peraturan2
PSK (Pre-shared-key): think this as a password or key to enter a door…password being said must exactly same like password remembered by door guard (key also…must match in order to unlock the door), lawannya PSK? Digital Certificate
Digital Certificate: tired remembering all the password for site A, site B, site C, and so on…?? Or exhausted from bringing all keys in “Key-chain” to unlock all the doors?…this is the solution, it like ID Card for US…as long as You (as ID Card bearer) and Door Guard recognize the Card (who made it of course) then you ready to go…
PKI (Public Key Infrastucture): this is a framework explaining how to create digital certificate, which mentioned above
CA (Certificate Authority): ini server yang bikin digital certificate, dia yang bikin, dia juga yang verifikasi keasliannya
RA (Registration Authority): ini optional, klo lu mau CA cuma bikin sertifikat dan yang nge-cek validitasnya server lain…si RA ini untuk ngecek validitas certificate-nya
CRL (Certificate Revocation List): ini serial number-nya certificate…di dalemnya ada masa berlaku ini sertifikat (expiry date)
SCEP (Simple Certificate Enrollment Protocol): Cisco punya, kek PKI Framework-nya Cisco…simple, Cuma pake HTTP untuk ngirim dan nerima request dan sertifikat
NAT-T (NAT Traversal): NAT and IPsec is not compatible each other, NAT itu kan ganti IP…jelas akan break salah satu rules dari VPN yaitu integrity (make sure data hasn’t been changed). NAT-T ini bikin header UDP di”depan”nya IPsec…jadi yang dibaca UDP NAT-nya dulu bukan IPsec-nya…both side harus aware klo mereka pake NAT-T (bahasa mudahnya…2-2nya harus dienable NAT-T klo mau pake VPN). Workaround for NAT-T? just use IP PUBLIC on your Firewall/Gateway
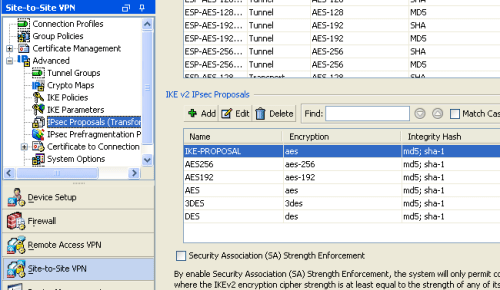
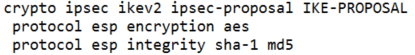
SA (Security Association): men-define mau pake apa enkripsinya, integritynya (hashing), bikin key sama tuker2annya mau pake apa
- Encryption mode: aes, des, 3des
- Hashing mode: md5 atau sha
- Key exchange mechanism: DH = diffie-hellman, all variant
- Expiry date untuk key-nya
Transform Set: isinya adalah metode yang akan digunakan oleh IPsec…mau pake ESP apa AH
PFS (Perfect Forward Secrecy): ensure itu VPN peer ga make key yang sama klo mau bikin session VPN baru
ESP (Encapsulation Security Payload): defined in RFC 4303 using IP Protocol* 50, isinya bagaimana caranya kita bisa authenticate dan encrypt itu traffic lewat VPN
IP Protocol: tipe2 sub-protocol didalam IP itu sendiri, contoh: 50 – ESP, 51 – AH, 46 – RVSP buat QoS, dll…(link)
AH (Authentication Header): more fast but less secure than ESP, only authenticate header with no encryption
DPD (Dead Peer Detection): teknologi untuk memastikan VPN peering kita ga down…kek IP SLA-nya VPN lah (default di IKEv2 sudah bisa setting ginian, ga perlu konfigurasi khusus kek di IKEv1)
EAP (Extensible Authentication Protocol): sebuah framework untuk extend PPP protocol yang mengatur bagaimana caranya mengauthentikasi user (bisa pake password, AAA, LEAP-nya Cisco, EAPOL-nya ethernet LAN, dll)
SPI (Security Parameter Indexes): mekanisme identifikasi SA ke packet yang datang (besarnya 32 bit)
——————–
References:
ISAKMP – https://tools.ietf.org/html/rfc2408
IKE – https://www.ietf.org/rfc/rfc2409.txt
Security Architecture for IP – https://tools.ietf.org/html/rfc4301
IPsec – https://tools.ietf.org/html/rfc4303
IKEv2 – https://tools.ietf.org/html/rfc4306
IKEv2 Updated – https://tools.ietf.org/html/rfc5996
http://www.h-online.com/security/features/A-death-blow-for-PPTP-1716768.html
https://tools.ietf.org/html/draft-ietf-ipsec-ikev2-tutorial-01
http://security.stackexchange.com/questions/56434/understanding-the-details-of-spi-in-ike-and-ipsec
https://supportforums.cisco.com/document/21746/what-extensible-authentication-protocol
https://en.wikipedia.org/wiki/List_of_IP_protocol_numbers
CCNP Security SIMOS powerpoint slide